Capture The Flag
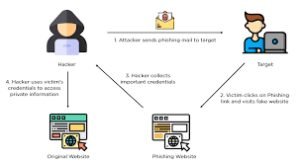
🖼️ CTF Challenge — Hidden in Plain Sight
A collection of images has been shared.
At first glance, they appear ordinary.
But experience tells us that ordinary files often hide extraordinary intent.
Not every image demands attention.
Some are merely noise.
Some whisper—but say nothing of value.
A few, however, carry meaning beneath their surface.
Those who rush will extract everything.
Those who think will extract what matters.
The truth is not buried deep.
It is subtly embedded — waiting to be noticed.
From fragments, a message emerges.
From individual words, a single phrase is formed.
That phrase is your flag.
Objective
- Identify the images that contain meaningful hidden data
- Extract the hidden words
- Arrange them correctly to reveal the final flag
Constraints
- You are allowed to use only one tool
- OpenStego
- No other tools, online services, or viewers are required
- Not every extraction leads to the flag
Flag Format
- A meaningful English phrase
Time Limit
- 20 minutes
Think carefully.
Extract selectively.
Trust logic over assumption.














🕶️ CTF Challenge — Phantom Behind the Pixels v1
A still frame has been shared — but not all is as it appears.
Some secrets aren’t buried deep... just subtly placed.
A simple gesture, often overlooked, might unveil hidden layers.
Look not within the image, but around it.
Sometimes, truth is revealed by what’s written in its shadows.
Upon discovery, you’ll encounter a cipher cloaked in ancestral digital wraps.
Let the base of all encodings untangle what’s been concealed.
🧬 CTF Challenge — The Unstable Rhythm v2
A sequence dances below — sporadic, unbalanced, yet deliberate.
But this is no ordinary encryption.
The title is the tempo, and the motion is nonlinear.
Before unravelling this ciphered thread, ponder the nature of movement:
erratic leaps, sudden reversals, repetition with purpose.
Some patterns don’t emerge until viewed in reverse… or disrupted.
🔍 Decoding this is not a straightforward descent.
You’ll need to jump between layers, as hinted by the structure of the code itself.
One layer speaks with symbols and order, the other with the full voice of alphanumeric balance.
Use the base bloodline. But don’t follow it blindly — let the motion of the name influence the method.
DECODE THIS
1meWAmpsczpGByO5NBWwWlGq8jddqssUPtQzA4Gt7fXyqtxc3OyXKwpIZeWkQeVtQX5tdbopbORchqQ8piJ4ltcMTOZpKTDFK4PbO6I0qsdPVy2OQf1oXAmS9cC7MIbIzldC3S9lfvgrNlKbCy2j15F70Oc1sYkkLR4qM9DKAoQeXC1boZ03bpmITc
🕵️♂️ CTF Challenge — Shadow in the Frame v2
A visual trace has been intercepted — an image cloaked in misdirection. 🖼️
Your task is to unveil the true entity lurking beneath the pixels.
🧩 This isn’t about what you see. The truth lies between the bits.
Analyze with discretion — tools that see the unseen may reveal more than meets the eye.
💡 Once you’ve unearthed the buried truth, you'll find it... oddly encoded.
Let the ancestral lineage of digital transformations guide your path to clarity.
🌀 CTF Challenge — Echoes of Jumping Jack v1
Below lies a tangled string of whispers — but the key to unlocking its message has already been shared.
Hidden not in code, but in concept.
The title is not just a label… it’s your first and final hint.
Think in loops, in reversals, in chaotic leaps — not all decoding is linear.
🔓 Decoding this cipher requires an ancestral method — those of the base kind.
But not all "base" types are the same. One bends to upper order, the other invites the full trio — digits, uppercase, and lowercase.
Let your interpretation of movement — back and forth — guide the sequence of unravelling.
DECODE THIS
KMYFMYKSIZGTCU32JJEFI222JBKVM4CEKNKXIYKXNRNFIVRQJZKFIMCKKNJEKVSPKJDFES2SNNLEQV2UKZKVEVLUJ5IWWYZQK5LEUVKTGBNFKVTLMRHFKMLEJBLGWZCIKUYUMTKTNN2E6UZRKJCFK22OKNKUK4CEKZCWYVKTGBLEWUTKKJLE23CKIRJWWZCHKRCWIVSVNN4EW===